Generating a .pem certificate from your .cer file to pass on to the server developer
suggest change- Save aps.cer to a folder
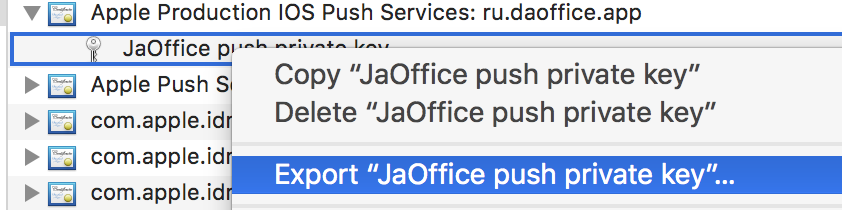
- Open “Keychain access” and export the key that is under that certificate to a .p12 file (call it key.p12). To do that right click on it and choose Export. Save it to the same folder as step 1. On export you will be prompted for a password. Make something up and memorize it.
- cd to that folder in Terminal and execute the following commands:
- Convert .cer to a .pem certificate
openssl x509 -in aps.cer -inform der -out aps.pem- Convert your key to .pem format. To open the key, enter the password you exported it with from the keychain, in step 2. Then, enter another password that will protect the exported file. You will be prompted to enter it twice for confirmation.
openssl pkcs12 -nocerts -out key.pem -in key.p12
- Merge the files into one final file
cat key.pem aps.pem > final_cert.pem
- The final_cert.pem is the final result. Pass it on to server developers with the password from step 5, so that they will be able to use the protected certificate.
Found a mistake? Have a question or improvement idea?
Let me know.
Table Of Contents